Foreign National Business Formation and the EB-5 Visa Process in Colorado
Foreign National Business Formation and the EB-5 Visa Process in Colorado
Congress, in its quest to keep our economy healthy, looks for ways to invite business owners and entrepreneurs from other countries here, to our shores, to build, manufacture, and employ our citizens. The good news, if you are a foreign national looking for a chance to become a U.S. business owner, is that you don’t have to be a multi-national conglomerate to own a business here in the United States.
USCIS administers the EB-5 program, created by Congress in 1990 to stimulate the U.S. economy through job creation and capital investment by foreign investors.
The EB-5 program doesn’t restrict visas to large corporations like Toyota and Siemens. Instead, it requires foreign investors invest in a new commercial enterprise or rescue a troubled business where they will continue to employ the existing employees for at least two years.
U.S. Citizenship and Immigration services (USCIS) describes new commercial enterprise as for-profit activity formed for the ongoing conduct of lawful business including by not limited to:
- A sole proprietorship
- Partnership (whether limited or general)
- Holding company
- Joint venture
- Corporation
- Business trust, or
- Other entity, which may be publicly or privately owned
There are a few catches, but if you can overcome them, you can set up shop in the United States as a foreign national. What seem to be the more challenging requirements? You have to be able to hire or employ 10 qualifying employees, and you need to be able to invest a substantial amount of capital.
A Foreign National Owned Business Must Provide Employment for 10 Qualifying Employees
Keeping in mind that the qualifying employees can be existing employees, as an Eb-5 foreign national owned business you must provide employments for 10 qualifying employees. A qualifying employee is described by USCIS as follows:
A qualifying employee is a U.S. citizen, lawful permanent resident or other immigrant authorized to work in the United States including, but not limited to, a conditional resident, a temporary resident, an asylee, a refugee, or a person residing in the United States under suspension of deportation.
However, “this definition does not include the immigrant investor; his or her spouse, sons, or daughters; or any foreign national in any non-immigrant status (such as an H-1B non-immigrant) or who is not authorized to work in the United States.” Which means your family can of course come with you, but if you hire a friend or family member who is also a foreign national, their job may not count toward the requirement to employ ten qualified people.
EB-5 Capital Investment Requirement
The EB-5capital investment requirement is pretty steep, but you can cut the amount required in half if you are willing to invest in a High Unemployment or Rural Area. The minimum general qualifying investment amount is $1 million, but the investment requirement in a Targeted Employment Area (High Unemployment or Rural Area) is on only $500,000.
There are a lot of rules and requirements that extend beyond this surface explanation, but if you are a foreign national who has a business idea or an entrepreneurial skill set that you believe would prosper well in the United States, it is worth your time to talk to an attorney who is familiar with the law and has experience preparing EB-5 visa applications.
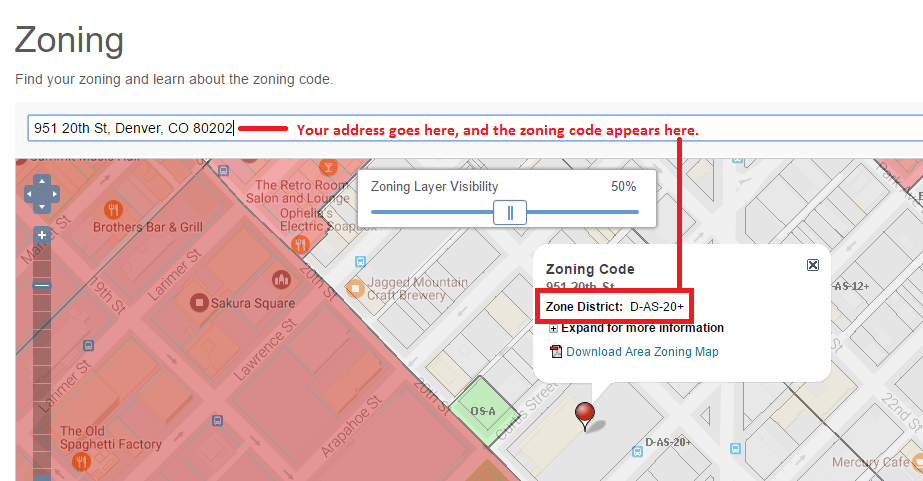
Foreign National Business Formation in Colorado
Our state, like many U.S. States, has a Regional Investment center designed to attract Foreign National business formation in Colorado. The Colorado Regional Center describes EB-5 investment as “an alignment of interests” which allow immigrant investors the opportunity to “live, work, attend school, or retire anywhere in the U.S.” Their website lists a host of benefits, including a path to citizenship if that is your ultimate goal.
- The investor does not have to be sponsored
- The process for approval is relatively fast compared to other visa programs
- The investor has more freedom of travel
- The investor has increased US educational opportunities (including residency benefits for dependent students) and
- The investor has the opportunity to become a U.S. citizen after five years
The EB-5 visa program is thriving in Colorado, and many areas of the state are welcoming and diverse, making it a popular alternative to more expensive East and West coast investment possibilities. If you are a foreign national with an interest in investing in or operating a business here in the United States, or have questions about foreign national business formation and the EB-5 visa process in Colorado, contact me, Elizabeth Lewis, at the Law Office of E.C. Lewis, P.C., home of your Denver Small Business Attorney. Phone: 720-258-6647. Email: elizabeth.lewis@eclewis.com
Contact Us Today
Law Office of E.C. Lewis, P.C.
Your Denver Business Attorney
LICENSED IN COLORADO AND NORTH CAROLINA
Mailing Address:
501 S. Cherry Street, Suite 1100
Denver, CO 80246
720-258-6647
Elizabeth.Lewis@eclewis.com